Tucked away in the latest high-end boards from ASUS, MSI, and Gigabyte, lies a new soldered-on component, i.e., an NPU (Neural Processing Unit).
It is marketed as a convenience feature, a way to enable clever optimizations like AI overclocking or network traffic prioritization.
But the more I dig, the more I see a permanent, un-auditable surveillance device embedded at the heart of our systems.
And frankly, it is a privacy nightmare waiting to happen.
The Below-The-OS Watcher You Cannot See
For starters, a motherboard NPU has Direct Memory Access, or DMA.
In plain English, this means it can read and write data directly to your system RAM without involving your CPU at all.
Your CPU, and by extension your operating system and all its security tools, simply do not see it happening.
The ARM developer documentation for embedded NPUs reveals the reality.
It states plainly that “there is no protection provided for privileged or unprivileged memory access from the NPU.”
It goes on to recommend that the NPU “should be made available to unprivileged software, only if the risk of unprivileged software accessing privileged memory is acceptable”.
Let that sink in.
The very architecture of these embedded AI chips treats memory protection as optional.
They are designed with a level of system access that would make any security engineer blanch.
The “Optimization” Trojan Horse: Convenience At What Cost?
Manufacturers pitch these NPUs as magical problem solvers.
For example, ASUS talks about “AI Overclocking” that learns your cooling capabilities.
In another instance, MSI advertises “AI Lan Manager” that prioritizes gaming traffic.
These features sound helpful. But think about what they require to function.
For starters, AI Overclocking needs constant monitoring of your voltage readings, clock speeds, and thermal data.
Moving on, AI LAN Manager requires deep packet inspection, meaning it analyzes the content of your network traffic in real time.
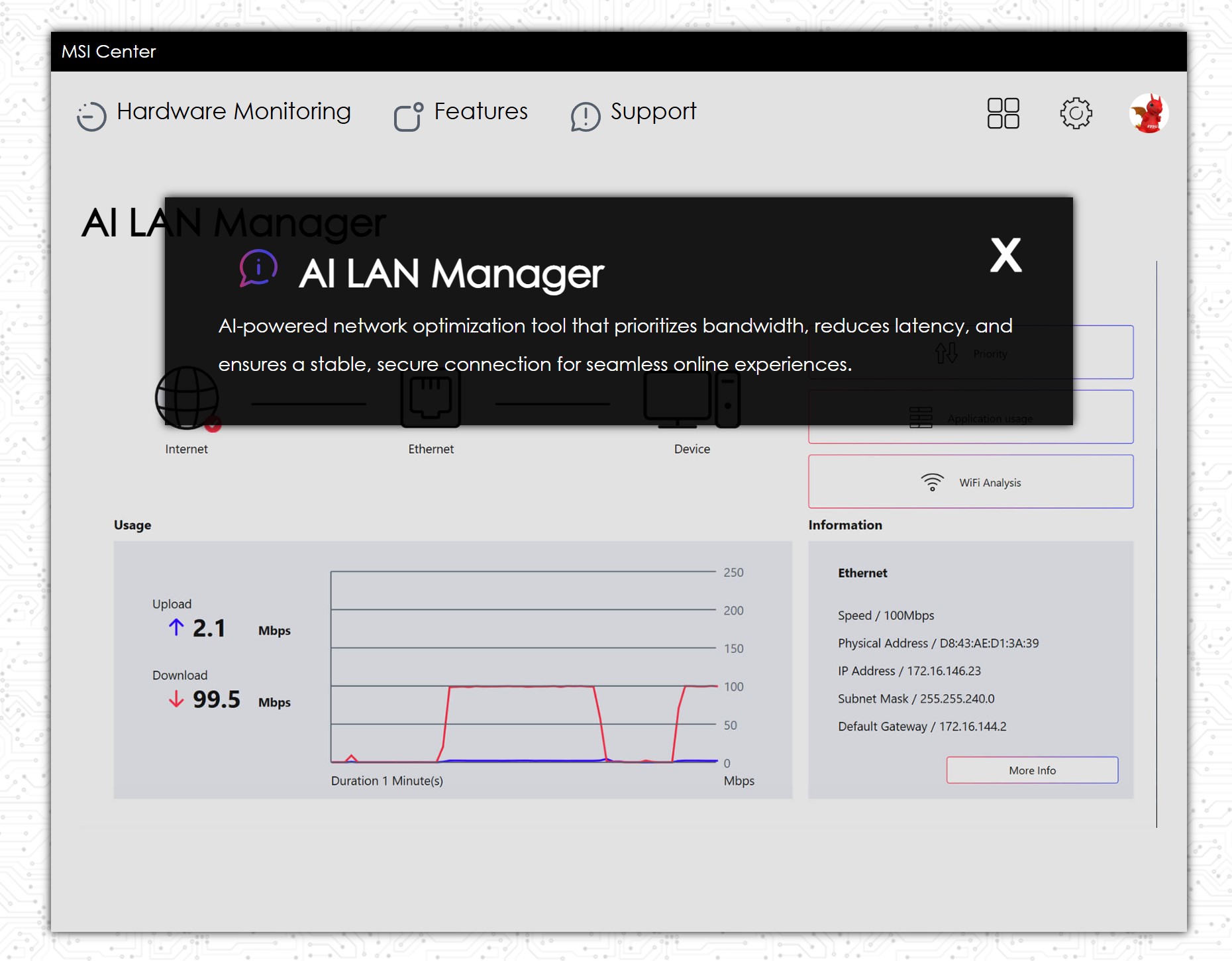
Where does all this behavioral data go?
Is it processed entirely on the NPU and then discarded?
Is it stored in firmware?
Is any of it, even aggregated anonymized telemetry, sent back to the manufacturer?
There are no answers. The process is opaque. The data path is invisible.
We are essentially installing a black box on our motherboards that has unfiltered access to our system’s most intimate operations, all in exchange for a slightly more convenient overclocking experience?
The Zero-Day Time Bomb: A Hacker’s Dream Backdoor
Any hardware component with this level of system privilege is a massive attack surface.
To put this into perspective, security researchers from Baidu Security demonstrated this starkly at Blackhat Europe 2023.
They presented research titled “Attacking NPUs of Multiple Platforms,” where they systematically explored the security of NPUs in devices from Samsung, Apple, and Qualcomm.
Their findings were alarming.
Firstly, Baidu Security discovered that the very complexity of NPU communication, from DMA mapping to command queuing, introduces a cascade of potential vulnerabilities.
Moreover, they were able to successfully execute arbitrary code on NPUs and even escalate privileges within the Android system.
What’s worse is that this research focused on mobile NPUs.
Motherboard NPUs, with even deeper system integration, present the same risks amplified.
The Evidence Is Already In The CVE Database
Unsurprisingly, the CVE (Common Vulnerabilities and Exposures) databases are already filling with NPU-related vulnerabilities.
To begin with, CVE-2023-33114 revolves around a memory corruption issue in an NPU that could lead to system compromise or data leakage.
Secondly, CVE-2024-33037 involves an NPU firmware flaw where invalid messages can leak information.
Even Intel, a major proponent of on-device AI, has had to patch multiple NPU driver vulnerabilities, including CVE-2025-35992 and CVE-2025-32735, which could allow denial of service or privilege escalation.
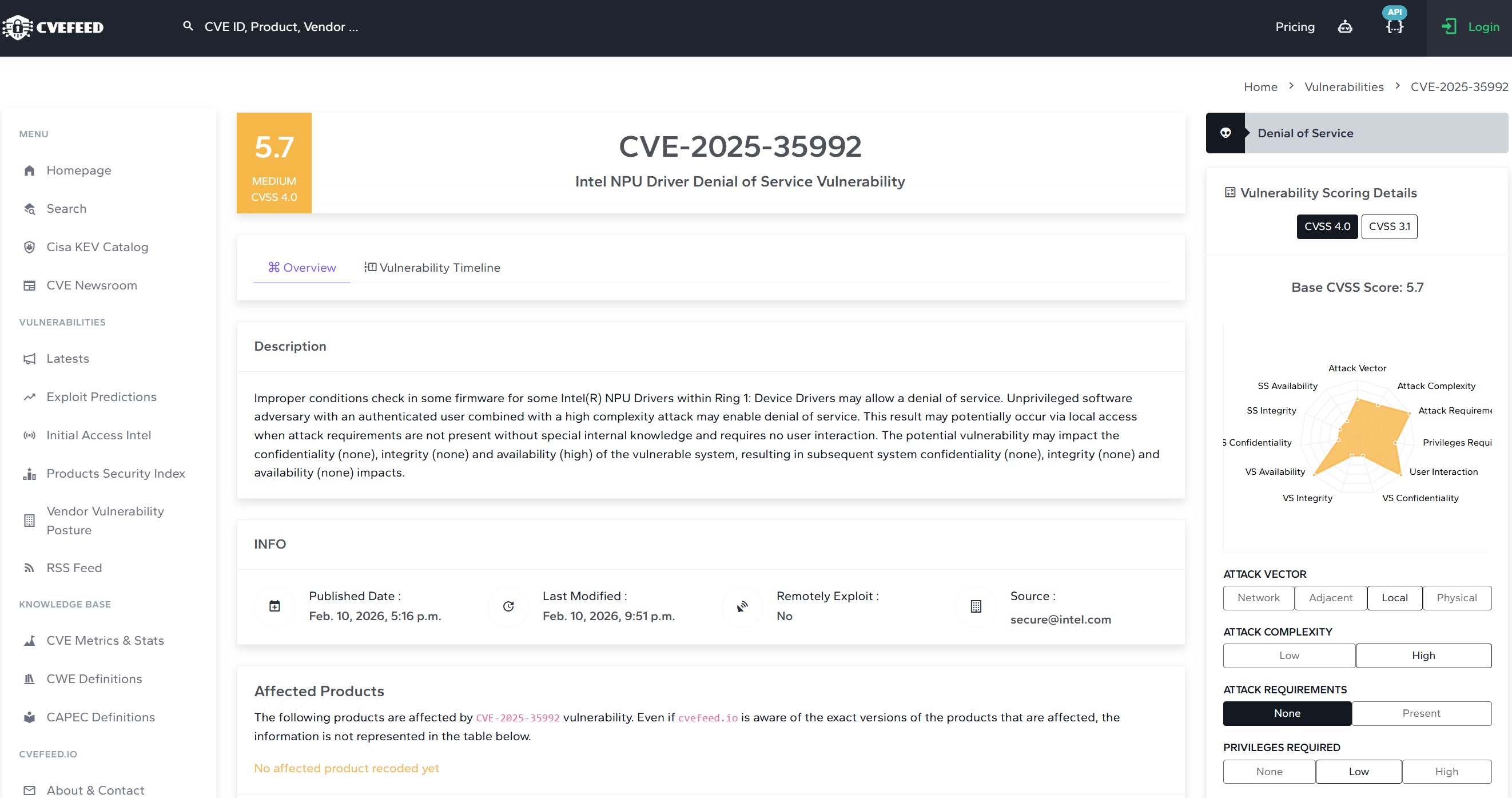
The pattern is unmistakable. NPUs are complex, privileged, and vulnerable.
An exploit targeting the motherboard NPU would be the ultimate backdoor.
It would operate below the OS, invisible to every security tool you run.
A skilled attacker could plant firmware-level malware that persists across reinstalls, reads every keystroke, exfiltrates every file, and you would never know.
The Path Forward: Demanding Transparency And Control
The industry is hurtling toward an AI-enabled future, so NPUs aren’t going to disappear anytime soon.
But we, as consumers and builders, must demand fundamental rights over these components.
We need transparency. Manufacturers must disclose exactly what data these on-board NPUs collect, how it is processed, and whether any of it leaves the system.
We need control. There must be a way to disable these NPUs at the firmware level, completely and verifiably, for users who do not consent to always-on AI monitoring.
We need accountability. Hardware security researchers must have access to audit these NPU implementations, and manufacturers must commit to rapid, transparent patching when flaws are discovered.
After all, your system’s most sensitive data deserves better protection than a marketing slide.
Thank you! Please share your positive feedback. 🔋
How could we improve this post? Please Help us. 😔
[Wiki Editor]
Ali Rashid Khan is an avid gamer, hardware enthusiast, photographer, and devoted litterateur with a period of experience spanning more than 14 years. Sporting a specialization with regards to the latest tech in flagship phones, gaming laptops, and top-of-the-line PCs, Ali is known for consistently presenting the most detailed objective perspective on all types of gaming products, ranging from the Best Motherboards, CPU Coolers, RAM kits, GPUs, and PSUs amongst numerous other peripherals. When he’s not busy writing, you’ll find Ali meddling with mechanical keyboards, indulging in vehicular racing, or professionally competing worldwide with fellow mind-sport athletes in Scrabble. Currently speaking, Ali’s about to complete his Bachelor’s in Business Administration from Bahria University Karachi Campus.
Get In Touch: alirashid@tech4gamers.com